from the good(?)-guys-with-guns??? dept
Cops keep letting us know who they really are. They can’t seem to help themselves.
They demand to be viewed as good guys, but far too often, they align themselves with fascists, racists, and opportunistic politicians who align themselves with fascists and racists.
When the latest presidential election delivered a loss to Donald Trump, his supporters chose to embrace the conspiracy theories their main man in office embraced. It was rigged. Votes were stolen. Everyone other than his supporters were wrong, perhaps so wrong they could be arrested.
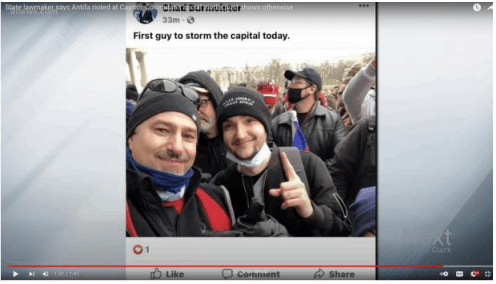
The opposite was true. While these supporters embraced theories espoused by 4chan users and played the part of the choir being preached to, the rest of the nation moved on. The supporters did not. They raided a federal building and to remove the word “peaceful” from the phrase “peaceful transition of power.”
Many of those are now facing federal charges. One of the instrumental groups in the failed insurrection was the Proud Boys, a self-described group of “Western chauvinists,” something that sounds much more socially acceptable than the phrase “white supremacists.”
But that’s what the Proud Boys are. They claim they aren’t because they don’t specifically prohibit non-whites from joining their pathetic group. They also pointed to their leader — Enrique Tarrio — as evidence of their non-racism. But ever since their inception, the group has chosen to support and advocate for the most racist of politically aspirational racists. And the group apparently simply couldn’t handle having their Racist-in-Chief being voted out of office.
But even before the Proud Boys conspired to assist in a raid of the Capitol building during the certification of election votes, it was still awful. Members of the group routinely ganged up on anyone they perceived to be against whatever the fuck it is that Proud Boys actually believe. (For all we know, it may just have been someone approaching a living, breathing woman during daylight hours.)
The Proud Boys are a joke. Members should feel embarrassed just to be associated with each other. But the members of this group have managed to turn individual insecurity to group insecurity by normalizing being absurd on main into a feature, rather than a bug. This group’s proprietary blend of incels and whites with bad haircuts had repeatedly failed to generate any sympathy for the group, much less its poorly stated goals.
But somehow cops still like the Proud Boys. And that says a lot about cops. Law enforcement in this nation transformed from a limited power circumscribed by the nascent Constitution to a rogue squad bent on retrieving free labor for plantation owners in less than 100 years. Law enforcement has never recovered from this perversion of its original intent. Cops hate free thinkers, liberals, non-whites, and people who think all of these groups should be treated with more respect.
That leads us to this: an indictment [PDF] brought against DC Metro Lieutenant Shane Lamond. As a member of the DC police force, Lamond was expected to protect federal targets from criminals and terrorists. As the head of the Metro PD’s Homeland Security Intelligence Branch, Lt. Lamond was expected to do even more. He was heading the bulwark against terrorists, foreign interference, and any other criminal activities that posed a threat to federal agencies and the physical property housing them.
Lt. Lamond was given a lot of power and a lot of trust. But he abused all of that to side with a bunch of guys who can’t talk to women and/or compose a coherent mission statement. Instead of protecting the nation via his position with the DC police force, he chose to inform alleged criminals that cops were looking for them, apparently in hopes of helping lawbreakers elude law enforcement.
This wasn’t a one-off thing. This indictment may only detail one obstruction of justice, but it also shows Lt. Lamond was buddying up with matching-hat-wearing weirdos for reasons he’ll soon have to explain to a judge.
Beginning in July 2019 and continuing to at least January 2021, LAMOND and Tarrio were in regular contact regarding the Proud Boys” planned activites in the District of Columbia. They communicated at least 500 times using cloud-based messaging services, including Google Voice, Apple Messages, and Telegram, an encrypted messaging application.
“Tarrio” is Enrique Tarrio, the presumed leader of this band of sexless, violent misfits. In this case, Tarrio was allegedly warned by Lt. Lamond law enforcement was seeking to arrest him for an alleged hate crime, the burning of a Black Lives Matters banner stolen from a DC church.
This warning didn’t work. Tarrio was arrested and convicted. As part of his plea deal, Tarrio (a longtime federal informant with a history of illicit drug dealing) agreed to stay out of Washington, D.C. As history shows, he violated this agreement and is now facing federal charges for his participation in a conspiracy (with his proudest boys) to raid the Capitol building.
So, this horrible person who (allegedly) played a part in stealing and burning a Black Lives Matter banner and who (allegedly) participated in a conspiracy to overthrow the part of the government tasked with certifying election results was apparently (and — I’ll say it now so I don’t get sued by Lt. Lamond — allegedly) someone the Metro PD official sitting at the head of Homeland Security Intelligence felt was worth his time and attention, not to mention his (alleged) leaking of sensitive law enforcement info in hopes of assisting Tarrio in evading arrest.
For example, on July 8, 2020, using Telegram, LAMOND notified Tarrio that a bar in Washington, D.C. frequented by Tarrio and members of Proud Boys might be subject to sanctions after an Alcohol and Beverage Control violation was reported. LAMOND informed Tarrio, “I’m working on finding out what sanctions might be imposed. As soon as I find out I will let you know.”
On November, 2020, vote counts revealed that resident Joseph R. Biden had won the 2020 Presidential Election, and several news organizations began reporting this fact.
At 1:08 pm on November, 2020, LAMOND texted Tarrio, “Hey brother,sad, sad news today. You all panning anything?” Tarrio responded, “Yep.”
At 2:10 p.m.on November 7, 2020,using Telegram, LAMOND told Tarrio that “Need to switch to encrypted. Alerts are being sent to LE that [Social Media Website] accounts belonging to your people are talking about mobilizing and ‘taking back the county. [sic] Getting people spun up. Just giving you a heads up.”
At 2:14 pm. on November 7, 2020, using Telegram, Tarrio sent LAMOND an audio message.
At 2:16 p.m. on November 7, 2020, using Telegram, LAMOND told Tarrio, “Got your voice messages. Just giving you a heads up. Please keep this between you and me.”
On November 13, 2020, Tarrio came to Washington, D.C. to attend a rally scheduled for the next day to contest the results of the 2020 Presidential Election.
Earlier on November 13, 2020, LAMOND texted Tarrio, “I’m staying in D.C. tonight. Let me know if you go out and I may stop by.”
After Tarrio later told LAMOND that he was heading to a bar in Washington, D.C., frequented by members of the Proud Boys, LAMOND responded, “Check telegram.”
Around the same time, on Telegram, LAMOND told Tarrio, “Just giving you a heads up there’s a lot of attention at [the bar] right now. If it doesn’t calm down they are going to shut [the bar] dow[n].” A short time later, LAMOND told Tarrio through Telegram, “Just wanted to let you know. I heard[the District of Columbia Alcoholic Beverage Regulation Administration] already on scene.”
On December 11, 2020, Tarrio and other members of the Proud Boys were in Washington, D.C., in advance of a rally planned for December 12, 2020, to protest the results of the 2020 Presidential Election. That evening, Tarrio, using Telegram, informed LAMOND that Tarrio and members of the Proud Boys were “going to have a briefing tonight at 1030 at the national mall” and that they were marching from a hotel in Washington, D.C. LAMOND responded, using Telegram, “Copy. Antifa should be staying up at BLM Plaza. Do you want me to let our uniformed officers know that or keep it to myself? I will be around all night in case: anything kicks off.”
So, pretty much BFFs: the would-be insurrectionist and the DC supervisor directly in charge of preventing bad things from happening to Washington, D.C.
That’s the meat of the indictment. These guys were about as close as internet friends can be, something that culminated with Lt. Lamond warning Tarrio there was a warrant out for his arrest in the BLM flag-burning case.
This is all very fucked up. It had been obvious for months, if not years, the Proud Boys encouraged lawlessness to forward their extremely peculiar theories about state and federal governance. No cop ever should have sided with them, much less handed over confidential info. But that’s how cops are. They love the lawbreakers that align themselves with the (again) peculiar worldview far too many cops have: that might means right and, more importantly, white means right. That Tarrio wasn’t technically white makes no difference. He and his boys were committing acts and pushing propaganda that made it clear the group would throw its support behind any white bigot willing to give them an indirect pat on the head during national press conferences.
We don’t get the police we want. We probably don’t even get the cops we deserve. We just get the cops that embrace the worst parts of our society along with the powerlessness to do anything about it. This cop may ultimately be convicted, but he’s just one of thousands of bad apples currently roaming free: guys with guns and power but no moral compass, who are convinced this nation’s domestic terrorists are just good people trying to preserve the American way of life.
Filed Under: dc police, enrique tarrio, homeland security, insurrection, january 6th, proud boys, shane lamond